🛰️💡 Dear network 🚀⚔️
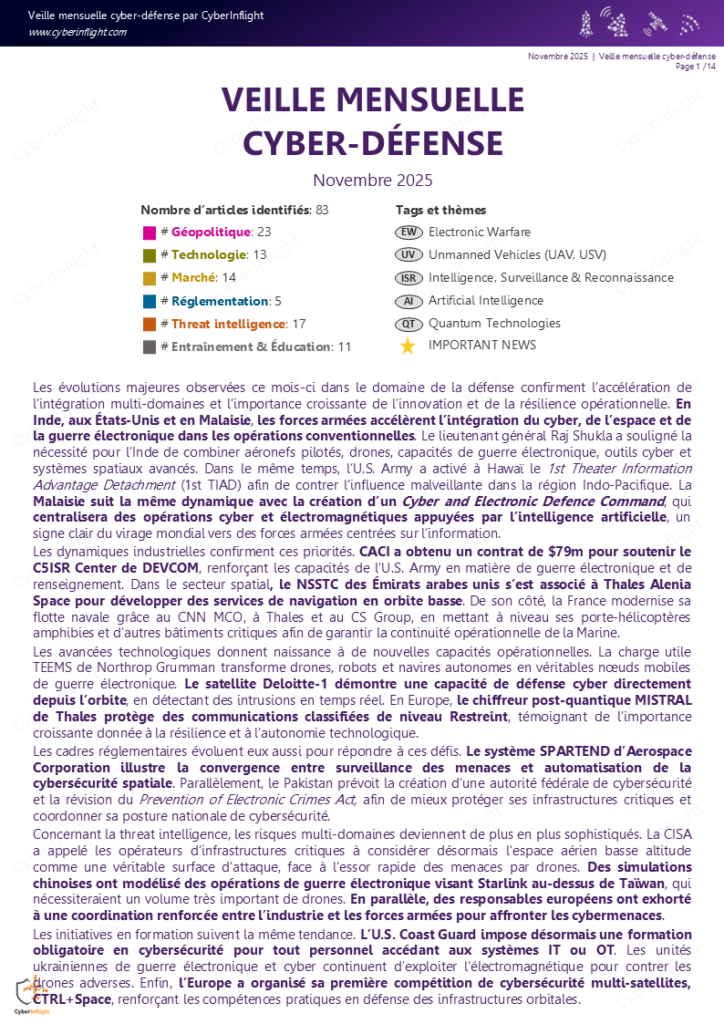
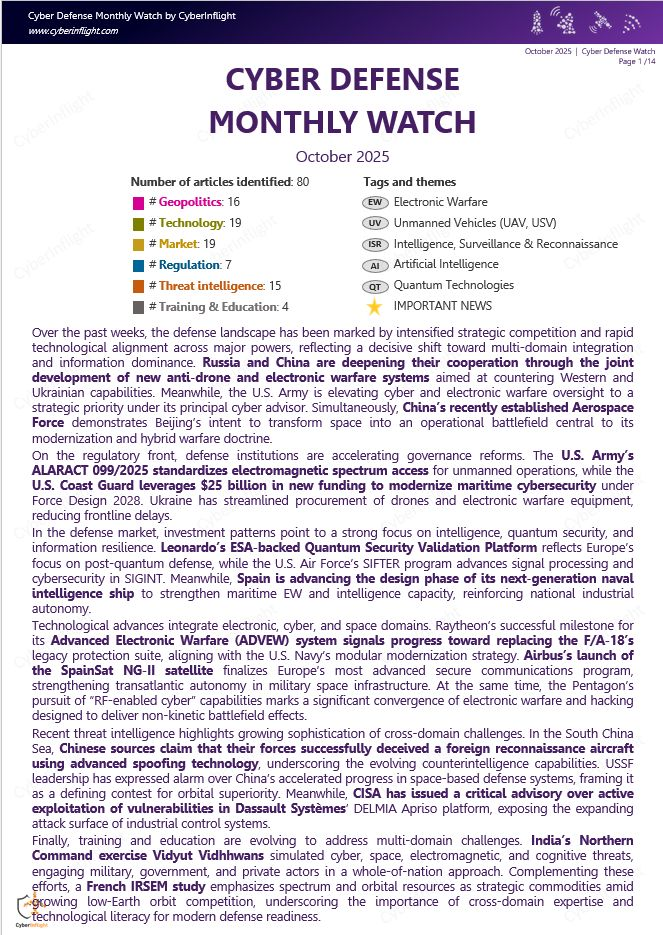
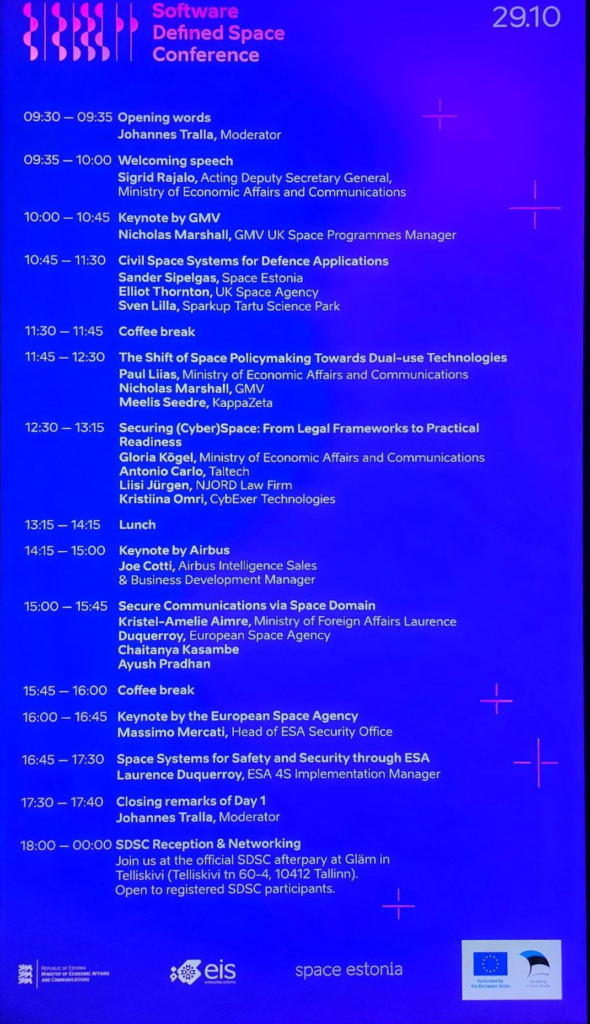
Yesterday at GovSatCom in Luxembourg 🇱🇺, one message was clear: space is now a warfighting domain.
As we enter the 5th year of the war in Ukraine 🇺🇦, the EU must step up through strong, sovereign, and resilient satcom initiatives. Connectivity is no longer a support function; it is a strategic capability.
Here are the key takeaways:
🔹 🌍 Space is a warfighting domain. It is fully embedded in modern defense strategy and operational readiness.
🔹 🛰️ LEO orbit is decisive, providing agility and resilience. At the same time, operators are betting on multi-orbit constellations and space-data relay architectures to ensure redundancy and enhanced performance.
🔹 💶 Barriers to entry (financial and procurement constraints) must be lowered to accelerate innovation and strengthen Europe’s competitive edge. Time to market matters.
🔹 ⚡ Satcom is fast-paced. Business and operational models are evolving toward a satcom-as-a-service approach, offering flexibility and scalability to governments and defense actors.
🔹 🇺🇦 Ukraine has been a real-life learning ground. The conflict has provided critical operational feedback (RETEX), helping improve resilience, deployment speed, and satcom security in real-world conditions.
The strategic shift is undeniable: resilience, agility, and sovereignty in space communications are becoming non-negotiable for Europe’s security future.
Thanks for the amazing conference GovSat !